Researchers have discovered a method to bypass the long-held “no-cloning theorem” in quantum mechanics, effectively allowing for the duplication of quantum information under specific conditions. The breakthrough, led by Achim Kempf at the University of Waterloo, demonstrates that qubits – the fundamental units of quantum computing – can be cloned, provided the information is encrypted with a single-use decryption key.
The No-Cloning Theorem and Its Limits
For decades, the no-cloning theorem has been a cornerstone of quantum physics. First established in the 1980s, it states that an unknown quantum state cannot be perfectly copied. Any attempt to measure and replicate the information inherently destroys the fragile quantum properties that make it valuable. This principle underpins many quantum encryption protocols, ensuring data cannot be intercepted and duplicated without detection.
However, Kempf’s team found a workaround: encrypting the quantum information before copying it. The encryption key is unique and disposable, meaning only one clear, unencrypted copy of the qubit can exist at any given time – preserving compatibility with the original theorem’s intent.
How Encrypted Cloning Works
The discovery stemmed from an investigation into quantum Wi-Fi, a concept previously considered impossible due to the no-cloning theorem. The team realized that random fluctuations (noise) in the system acted as a natural encryption mechanism, scrambling the original message while allowing for a reversible decryption process. By intentionally exploiting this noise, they devised a protocol to create multiple encrypted copies.
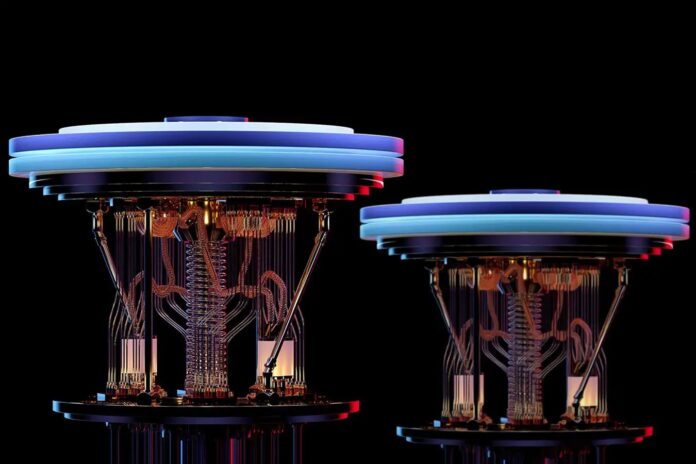
The method was tested on a real IBM Heron quantum computer, successfully generating hundreds of encrypted clones of single qubits. The team estimates they could produce over 1,000 before error rates become prohibitive.
Implications for Quantum Computing and Storage
This breakthrough has significant implications for quantum cloud storage and computing. As Kempf explains, the technique mirrors traditional data redundancy systems like Dropbox, where files are replicated across multiple servers to prevent data loss.
“If you send a file to Dropbox, it will save your data at least three times in three different computers that are geographically separated, so that if one is hit by fire, the other one by a flood, there’s a fair chance the third one survives. It used to be thought you can’t do that with quantum information, because you can’t clone it. But what we showed is that you can do it.”
Is It Really Cloning?
Some experts, like Aleks Kissinger at the University of Oxford, argue that this isn’t true cloning but rather a clever redistribution of quantum state. The process doesn’t create identical, independent copies; instead, it spreads the information among multiple parties, with only one ultimately able to fully recover it.
Kempf acknowledges the nuance, calling it “encrypted cloning” – a refinement, not a violation, of the original theorem. The key takeaway is that while perfect duplication remains impossible, secure replication of quantum information is now demonstrably achievable.
This discovery underscores the evolving understanding of quantum mechanics and its practical applications. While the method doesn’t break the fundamental laws of physics, it expands the possibilities for building more robust and reliable quantum systems.